The fight against vulnerabilities is a constant battle, a real race between hackers and organizations trying to keep them out. Unfortunately, organizations happen to lose.
On the one hand, consider that only a mere single vulnerability on one application could allow a hacker to compromise an infrastructure. On the other hand, organizations must make huge and expensive effort across the whole company’s scope to ensure a consistent cybersecurity posture. Hackers know most vulnerabilities and exploits before being published and patched giving them a head start. In addition, organizations face many challenges complicating the management of their vulnerabilities.
As ex-FBI Director Robert Mueller said, “… there are only two types of businesses: those that have been hacked and those that will be hacked.”
The vulnerability lifecycle
Find the lifecycle of a vulnerability below:

As soon as a vulnerability is discovered, the risk dramatically increases. From there, the risk even keeps on growing as the vulnerability becomes exploitable and more widely known. Risk decreases after a patch or an upgrade’s release. Indeed, Ops begin to patch the systems, which can take time for many reasons. For instance, because of a lack of information or staff to patch, the obligation to carry out a costly or risky project. Attacks exploiting vulnerabilities that have not been released or have no known patches are called zero-day attacks.
The nature of vulnerability publications can be very different and have diverse impacts. Good or bad actors can discover and publish them to the virtuous or malicious audience. In addition, editors’ time reaction to propose patches also greatly varies depending on the context (for instance, the technical complexity).
Organizations challenges
Organizations face many challenges when struggling with vulnerabilities:
- Allocating resources: organizations happen to lack available IT resources and processes to adequately design and execute an efficient vulnerability management program.
- Managing a high volume of data: organizations identify a high number of vulnerabilities in their network. They also spend most of the time structuring the data to extract valuable outputs, instead of orientating the effort on the security of their assets.
- Identify where the risk is located: prioritization and remediation plan often focus on assessing the criticality of the vulnerability, forgetting other factors such as the criticality of the asset itself and the potential business impact.
- Perform an efficient remediation program: as a security department can almost independently work on the prioritization plan, several departments must engage in the remediation plan within a common approach and objectives.
- Patching difficulty: mainly due to operational reasons, patching can be difficult or impossible.
- Maintain an up-to-date asset inventory: having an up to date and maintained asset inventory is a pain point for IT teams.
How to manage vulnerabilities?
 To build efficient vulnerability management it is important to understand how the business works and to identify the business processes and the assets supporting them. This risk-centred approach offers a view on the real criticality of vulnerabilities and permits an efficient prioritization of actions.
To build efficient vulnerability management it is important to understand how the business works and to identify the business processes and the assets supporting them. This risk-centred approach offers a view on the real criticality of vulnerabilities and permits an efficient prioritization of actions.
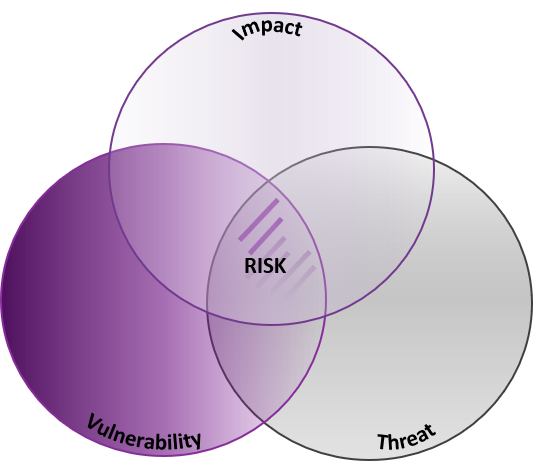
To identify business risks it is necessary to have a view on threats, vulnerabilities and their business impacts.
Excellium Services and Qualys recommend implementing a vulnerability management lifecycle consisting of the following steps:
- Discover Your IT Environment – ensure every network device and the software application that resides in the network is inventoried.
- Prioritize Your IT Assets – identify, visualize, and organize the network assets into Business Units and Asset Groups. Define the “mission-critical” assets by their importance to the business operations.
- Assess IT Security Vulnerabilities – scanners safely and accurately detect security vulnerabilities across the entire network in a highly automated manner.
- Report Threats with Powerful Analysis – using the Common Vulnerability Scoring System (CVSS) and the criticality of the assets agreed in the strategy definition. Reports provide both a detailed technical analysis (with a description for each vulnerability including the security threat, consequences of the exploited vulnerability, and the recommended solution to fix the vulnerability, including links to the appropriate patches and an executive-level summary.
- Remediate Your IT Vulnerabilities – prioritize actions to fix vulnerabilities according to the business risk.
- Verify effectiveness – The vulnerability system management tracks each vulnerability in the system until verifiably fixed.

What about you? How do you manage your vulnerabilities?
Gartner anticipate organizations using the risk-based vulnerability management method will suffer 80% fewer breaches by 2022. 1Source: Gartner, “Implement a Risk-Based Approach to Vulnerability Management,” Prateek Bhajanka, Craig Lawson, 21 August 2018. This prevision warns of the importance of implementing and upgrading a vulnerability management model to a Business-Risk based vulnerability management.

Did you like the article? Discover how Qualys and Excellium help you beat vulnerabilities.
Do not miss our next episode coming out soon.
#AboveVulnerabilities
Excellium Team.



